Have you used your quarterly review yet?
As an IT360 client, you have more than just technical support–– you have a dedicated tech advocate. Our partnership includes proactive quarterly reviews and strategic planning, during which your CSA (Client Success Advisor) partners with you to ensure your IT is both running smoothly and aligned with your business goals. Now’s the perfect time to schedule your Q3 tech roadmap session. These reviews go beyond troubleshooting—they’re designed to catch inefficiencies before they cost you time or money. From identifying outdated tools to streamlining software usage, your quarterly review could be the key to reduced spend and better productivity.

Whenever possible, avoid using public Wi-Fi entirely. It’s often unencrypted and an easy target for hackers looking to intercept passwords, emails, and other confidential information. If a public connection is your only option, be extra cautious: don’t access sensitive documents or log in to critical systems unless you’re using a secure VPN.How well do you know your IT? Here are some of the benefits you’re already receiving as an IT360 client:
Your IT360 portal has real-time ticket status updates. You’re never in the dark about where things stand.
Your backups are tested automatically every month. No need to wonder if you’re covered—we’re checking for you.
While we’re always looking out for your business with strategies like these, proactive check-ins keep your technology running smoothly. Let’s make sure your systems are supporting your success, not slowing you down. If you haven’t scheduled your Q3 review yet, now’s the time. Be sure to check your email and phone for a message from your CSA and set a time to make the most of your tech today.
Ask Rami:
Question: “Isn’t AI and Automations only for tech giants and large companies?”
Answer: Not anymore. Today’s AI and automation platforms are built to scale down as easily as up. Whether you’re a five-person team or a Fortune 500, you get the same core benefits. In fact, it’s often the simplest, lowest-level automations like streamlining emails, data entry, or basic reporting that deliver the biggest day-to-day impact. Small improvements quickly compound, making your whole team more productive.
About Rami:
Hello, my name is Rami. I graduated from Northern Illinois University in Dekalb, IL, with a bachelor’s degree in computer science. I continued my studies to earn a master’s degree in computer science, focusing on data analytics and AI. I am part of the AI & Automations team at IT360, where I help clients start their AI journey and build automations of all shapes and sizes, from custom solutions to implementing existing AI systems into their business. Outside of work and the constantly evolving landscape of AI, I enjoy spending time outdoors fishing (which is more like casting, because I don’t do much catching) and tinkering with electronics
Did you know?
World Wide Web Day is in August—a perfect reminder of how much we rely on the internet every day.
The average office worker spends over 6 hours a day on the web. That’s why reliable, secure connectivity isn’t optional—it’s essential. At IT360, we make sure your network can keep up with your team, your tools, and your goals—without compromising security.
CyberSecurity:
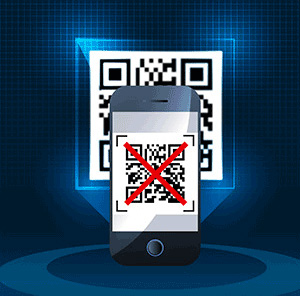
Cyber Alert: UNFI Supply-Chain Surge in QR Code Phishing Attacks – What You Need to KnowAttack Disrupts Grocery Retail
Cybercriminals are getting more creative—and QR codes are their latest tool. A rising threat called quishing (QR code phishing) is targeting users through fake QR codes embedded in emails, flyers, and even posters. When scanned, these codes can direct users to malicious websites designed to steal login credentials or install malware. Because QR codes often bypass traditional email filters and feel less suspicious, even savvy users are falling victim—especially in professional settings where QR codes are commonly used for check-ins, surveys, or payments.
To protect yourself and your team, avoid scanning QR codes from unknown or unsolicited sources, particularly in emails. If you’re on a desktop, hover over the link (when available) to preview the destination before scanning. And if you ever come across a suspicious QR code, report it to IT360—we can help validate and block harmful links.
Bonus tip:
Ask us about our phishing simulation training. It’s a fast, effective way to educate your team and strengthen your organization’s cybersecurity posture in under an hour. Stay smart, stay secure—and always think before you scan.
Project spotlight
IT360 recently partnered with a disability services and support organization to streamline and secure their mobile device management system. With 82 users and devices involved, the project focused on transitioning from Meraki to Hexnode, a cloud-based endpoint management solution. This upgrade empowered the organization with more robust and user-friendly tools to manage their digital workspace. Hexnode offers a range of features including simplified device enrollment, kiosk lockdown, baseline configurations, and remote monitoring—ensuring security and operational efficiency across various operating systems. The new system allows administrators to monitor and control devices with ease, ultimately supporting the organization’s mission through enhanced technology.



